Of The BPI (British Recorded Music Industry)
Still in his job [sigh].
Saturday 29 December 2012
Saturday 15 December 2012
Friday 14 December 2012
The Speed of Jean Sibelius
At The Castle Gate
If you've watched The Sky At Night religiously since the mid 1960s, then you've seen all but a few dozen of Sir Patrick's 700+ episodes. Alas, the ones you missed will probably have to stay missing, their tapes having been wiped or thrown out, if indeed they ever existed (many episodes were simply broadcast live).
You've also heard the opening strains of Sibelius's Pelléas et Mélisande a corresponding number of times, in this recording of the Royal Philharmonic Orchestra conducted by Sir Thomas Beecham. Such long term exposure to that introduction has, you've almost certainly found, two noticeable side effects. One is perfect pitch: at the close of a hi-hat you can sing its opening chord, bell clear and literally pitch perfect, at any time of any day or night. Man, that's got to be the world's most unbelievably annoying earworm. The second effect, and the one exercising me here today, is a very strong and ingrained opinion concerning exactly what tempo the piece should be played at.
 Sir Patrick's death last Sunday occurs as I'm completing the central corpus of a symphony collection, and turning to concentrate on other, equally non-vocal, classical musical forms. So naturally, I was prompted to add to the old Micro-SDXC card, this suite of incidental music written for Maurice Maeterlinck's 1892 drama of doomed infatuation. Turning to Amazon, I thought I'd spin the old amateur astronomer, virtuoso musician, composer and Krautbasher in his grave, by downloading this Deutsche Grammophon Masters recording of Berliner Philharmoniker, under the onetime Nazi maestro himself, the Austrian Herbert von Karajan.
Sir Patrick's death last Sunday occurs as I'm completing the central corpus of a symphony collection, and turning to concentrate on other, equally non-vocal, classical musical forms. So naturally, I was prompted to add to the old Micro-SDXC card, this suite of incidental music written for Maurice Maeterlinck's 1892 drama of doomed infatuation. Turning to Amazon, I thought I'd spin the old amateur astronomer, virtuoso musician, composer and Krautbasher in his grave, by downloading this Deutsche Grammophon Masters recording of Berliner Philharmoniker, under the onetime Nazi maestro himself, the Austrian Herbert von Karajan.
Now, I've had plenty of speed issues with certain grand maestro composers before, most notably Herr Herbert here, but also Sir Georg Solti, Leonard Bernstein, and a few others (by contrast, I always find Daniel Barenboim perfectly to taste). But sweet mother of Adolf, nothing in the history of music could ever have prepared me ever for the glacial interminability of this treatment, ever. Whatever the merits of the rest of the suite, that first geologically grinding movement is bloody unlistenable.
What's the Frequency?
Clearly at this point I had to know which was "right", in the sense of being closer to the composer's original intention. Because, you know, that can change everything. If this impossibly, inhumanly lento melodrama corresponded more faithfully to the thoughts of Jean Sibelius, then I'd just have to learn to live without Beecham's much more familiar dancefloor aerobic workout. Luckily we can decide these things independently. On Sibelius's original score, there's a tempo command specifying
which is to say: serious and ... widely? ... expansively I guess, with 48 minims (half-notes) per minute. The time signature is 2:2, so there are two minims in a bar, and the piece comprises 60 bars in total, with no repeats. Oh wait, two of those bars are in 3:2 time - Jean, you crafty devil! - so we'll call it 61 equivalent bars of 2:2 to compensate. That's a grand total of 122 minims, which at a mean frequency of 48 per minute, should take just 2 minutes and 32½ seconds to play.
Run time of the Karajan recording: six minutes dead.
Conclusion
So that settles it then. Just as I'd suspected, Herbert von Karajan was a grandstanding, temporising, scene-stealing, attention-seeking hack of a drama queen. Yes, I have indeed wasted my money with this purchase. And yet...
The funny thing is, once I found the score and followed it along with the music, this interpretation really started to grow on me. And you know, even the canonical Beecham stretched it out to 3½ minutes.
If you've watched The Sky At Night religiously since the mid 1960s, then you've seen all but a few dozen of Sir Patrick's 700+ episodes. Alas, the ones you missed will probably have to stay missing, their tapes having been wiped or thrown out, if indeed they ever existed (many episodes were simply broadcast live).
You've also heard the opening strains of Sibelius's Pelléas et Mélisande a corresponding number of times, in this recording of the Royal Philharmonic Orchestra conducted by Sir Thomas Beecham. Such long term exposure to that introduction has, you've almost certainly found, two noticeable side effects. One is perfect pitch: at the close of a hi-hat you can sing its opening chord, bell clear and literally pitch perfect, at any time of any day or night. Man, that's got to be the world's most unbelievably annoying earworm. The second effect, and the one exercising me here today, is a very strong and ingrained opinion concerning exactly what tempo the piece should be played at.
 Sir Patrick's death last Sunday occurs as I'm completing the central corpus of a symphony collection, and turning to concentrate on other, equally non-vocal, classical musical forms. So naturally, I was prompted to add to the old Micro-SDXC card, this suite of incidental music written for Maurice Maeterlinck's 1892 drama of doomed infatuation. Turning to Amazon, I thought I'd spin the old amateur astronomer, virtuoso musician, composer and Krautbasher in his grave, by downloading this Deutsche Grammophon Masters recording of Berliner Philharmoniker, under the onetime Nazi maestro himself, the Austrian Herbert von Karajan.
Sir Patrick's death last Sunday occurs as I'm completing the central corpus of a symphony collection, and turning to concentrate on other, equally non-vocal, classical musical forms. So naturally, I was prompted to add to the old Micro-SDXC card, this suite of incidental music written for Maurice Maeterlinck's 1892 drama of doomed infatuation. Turning to Amazon, I thought I'd spin the old amateur astronomer, virtuoso musician, composer and Krautbasher in his grave, by downloading this Deutsche Grammophon Masters recording of Berliner Philharmoniker, under the onetime Nazi maestro himself, the Austrian Herbert von Karajan.Now, I've had plenty of speed issues with certain grand maestro composers before, most notably Herr Herbert here, but also Sir Georg Solti, Leonard Bernstein, and a few others (by contrast, I always find Daniel Barenboim perfectly to taste). But sweet mother of Adolf, nothing in the history of music could ever have prepared me ever for the glacial interminability of this treatment, ever. Whatever the merits of the rest of the suite, that first geologically grinding movement is bloody unlistenable.
What's the Frequency?
Clearly at this point I had to know which was "right", in the sense of being closer to the composer's original intention. Because, you know, that can change everything. If this impossibly, inhumanly lento melodrama corresponded more faithfully to the thoughts of Jean Sibelius, then I'd just have to learn to live without Beecham's much more familiar dancefloor aerobic workout. Luckily we can decide these things independently. On Sibelius's original score, there's a tempo command specifying
which is to say: serious and ... widely? ... expansively I guess, with 48 minims (half-notes) per minute. The time signature is 2:2, so there are two minims in a bar, and the piece comprises 60 bars in total, with no repeats. Oh wait, two of those bars are in 3:2 time - Jean, you crafty devil! - so we'll call it 61 equivalent bars of 2:2 to compensate. That's a grand total of 122 minims, which at a mean frequency of 48 per minute, should take just 2 minutes and 32½ seconds to play.
Run time of the Karajan recording: six minutes dead.
Conclusion
So that settles it then. Just as I'd suspected, Herbert von Karajan was a grandstanding, temporising, scene-stealing, attention-seeking hack of a drama queen. Yes, I have indeed wasted my money with this purchase. And yet...
The funny thing is, once I found the score and followed it along with the music, this interpretation really started to grow on me. And you know, even the canonical Beecham stretched it out to 3½ minutes.
Wednesday 5 December 2012
SA1503: CurlyBracketsMustNotBeOmitted (Part 1)
Parenthetical Remarks
StyleCop rule SA1503 is designed to complain whenever
Syntactic Structures
In C#, the bodies (or consequents) of certain flow control and looping constructs, such as if, while, and for statements, can syntactically be any single statement. For example, the underlined statements below are all single-statement bodies:
Problem?
Some people point out that the indentation can be applied incorrectly, and that the resultant statement
A Bad Fix
Sadly, those same people who insist on allowing badly formed indentation to pollute their code, often compound their error by suggesting a rather odd way of fixing it. Simply disallow any statement type except a block in these contexts! The result is a proliferation of brackets:
Another Example
In the above referenced documentation of rule SA1503, the following example is given:
Preliminary Conclusion
When I started looking into this issue, I was inclined to accept switching on rule SA1503. Anecdotal evidence seemed to support the idea that it could prevent bugs. And then, for me at least, there was this clincher: even Eric Lippert appeared to be suggesting that compulsory braces represented a solution to the classic dangling else problem, and one which he wished had been applied to C# from day one!
Then I realised that SA1503 wanted to do much more than just enforce braces in an if statement where an else clause was present. It wanted braces everywhere! That was when I began to pay closer attention to the arguments being offered, both for and against the measure.
The faulty examples above are typical of much I've encountered in researching what now appears to me a particularly misguided and ineffectual StyleCop rule. In seeking to mitigate against bad code layout by making wholesale changes to its syntactic structure, we not only miss our target entirely, but find ourselves instead lowering the code quality and readability. SA1503 therefore seems a bad rule from this perspective.
Next time: quick edits & legacy code.
StyleCop rule SA1503 is designed to complain whenever
The opening and closing curly brackets for a C# statement have been omitted.What does this mean, and is it a good rule?
Syntactic Structures
In C#, the bodies (or consequents) of certain flow control and looping constructs, such as if, while, and for statements, can syntactically be any single statement. For example, the underlined statements below are all single-statement bodies:
Obviously there are times when you want the body of your construct to contain, rather than a single atomic statement, a sequence of two or more such statements. This is accommodated by the use a special type of single statement called a block, comprising just the required sequence of statements enclosed in curly braces, as shown below. Note that the entire contents of the curly braces, including the braces themselves, still comprise a single statement - which just happens to be of the block type:if (x == 1) y = 2; else z = 3; while (x < 10) x++; for (var i = 0; i < 10; i++) x *= i;
if (x == 1)
{
y = 2;
z = 3;
}
These flow control and looping constructs can be nested within one another. A simple example of such nesting is this:
if (A())
if (B())
C();
else
D();
Since the rule in C# is that an else clause gets associated with the nearest available if statement, the else in this example has been indented to line up correctly with the second if statement, to which it properly belongs.Problem?
Some people point out that the indentation can be applied incorrectly, and that the resultant statement
if (A())
if (B())
C();
else
D();
can be ambiguous. Of course it's not ambiguous; after all, the compiler has absolutely no problem in applying the correct rules of precedence in a case like this, and coming up with the one correct result. However, it is true to say the above example is confusing, since it looks as though the else clause refers back to the first if statement rather than matching the second. The obvious remedy is to correct the indentation - and in fact to enforce consistent and correct indentation in future, so that such confusion cannot occur.A Bad Fix
Sadly, those same people who insist on allowing badly formed indentation to pollute their code, often compound their error by suggesting a rather odd way of fixing it. Simply disallow any statement type except a block in these contexts! The result is a proliferation of brackets:
if (A())
{
if (B())
{
C();
}
else
{
D();
}
}
Although much harder to read, this version does at least have the virtue that its intention is quite clear. However, that clarity has not come about from the addition of braces. No, the alignment of the braces merely served to highlight the indentation error which was causing the confusion, and which incidentally has also been corrected in this latest version. Correct the indentation and we remove the confusion, braces or none. If anything, the braces are making it more difficult to follow the structure of nested statements like these, by making them twice as tall as they need be, and physically separating the components that you're trying to line up visually.Another Example
In the above referenced documentation of rule SA1503, the following example is given:
Okay, so far I'm agreeing with you. But sadly we soon descend into nonsense:if (true) this.value = 2; return this.value;
Glancing at this code, it appears as if both the assignment statement and the return statement are children of the if-statement. In fact, this is not true. Only the assignment statement is a child of the if-statement, and the return statement will always execute regardless of the outcome of the if-statement.
StyleCop always requires the opening and closing curly brackets to be present, to prevent these kinds of errors:Yeah, no. Now this so-called example lacks any credibility. Look, if that first fragment compiles, the one without the braces, then it must be sitting at the very end of its enclosing method - because it ends with an unconditional return, anything after which is unreachable code. Which of course you're already detecting, and in fact treating as an error, right? Right, so it's the last thing in the method. But this means that the second version can't compile at all, since there needs to be another unconditional return statement after it; the compiler will be justly livid about its absence (not all paths return a value, nag nag nag...).
if (true) { this.value = 2; return this.value; }
Preliminary Conclusion
When I started looking into this issue, I was inclined to accept switching on rule SA1503. Anecdotal evidence seemed to support the idea that it could prevent bugs. And then, for me at least, there was this clincher: even Eric Lippert appeared to be suggesting that compulsory braces represented a solution to the classic dangling else problem, and one which he wished had been applied to C# from day one!
Then I realised that SA1503 wanted to do much more than just enforce braces in an if statement where an else clause was present. It wanted braces everywhere! That was when I began to pay closer attention to the arguments being offered, both for and against the measure.
The faulty examples above are typical of much I've encountered in researching what now appears to me a particularly misguided and ineffectual StyleCop rule. In seeking to mitigate against bad code layout by making wholesale changes to its syntactic structure, we not only miss our target entirely, but find ourselves instead lowering the code quality and readability. SA1503 therefore seems a bad rule from this perspective.
Next time: quick edits & legacy code.
Thursday 29 November 2012
Your Feature Has Been Cancelled
Or At Least Postponed
Surely that calls for a Rage Comic? I suppose we'll find out next summer, whether there's still going to be any appetite for an Office 2007 style user interface.
Maybe the more interesting question is, will there even be a desktop then?!
Surely that calls for a Rage Comic? I suppose we'll find out next summer, whether there's still going to be any appetite for an Office 2007 style user interface.
Maybe the more interesting question is, will there even be a desktop then?!
Friday 2 November 2012
VUPEN Pwns Windows 8 & IE10
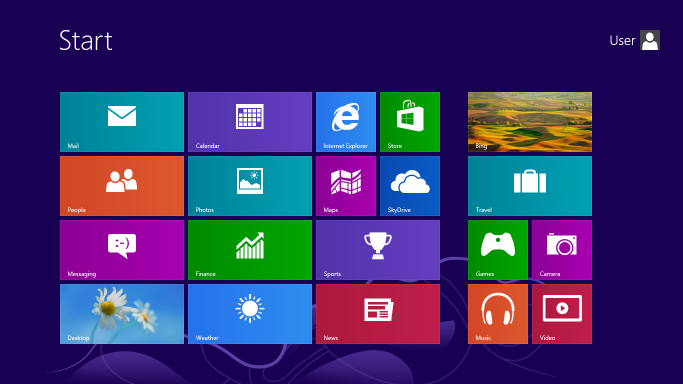 |
| Windows 8 (used with permission from Microsoft) |
Yes, already. But you're unlikely to hear much in the way of detailed descriptions of the multiple, preexisting zero-day vulnerabilities chained together to effect these new ones. That's because their discoverer is essentially a black hat: the French security firm VUPEN.
With all the talk about cyber security, cyber wars, and preemptive legislation coming from ploiticos east and west, you might have thought that governments would be among the first, and most willing, to condemn and criminalize a company like VUPEN. This is an organization whose business model is to discover security holes in the products of giants like Microsoft, Google, or Apple, then rather than disclose these flaws for patching, sell the information to the highest bidder for use in arbitrary attacks.
Follow The Money
Patching would make everybody safer, and increase our confidence in the various devices and services we have to use every day, but it doesn't carry the same high financial rewards as selling your knowledge to whomever wants to exploit it most. Meanwhile, those governments we rely on to make the best choices for us, to legislate and protect us, yada yada... well it turns out, those are exactly the kind of people who most desire the ability to intercept, spy on, record, even to corrupt or otherwise modify, our communications, activities, and sundry interactions with others. And, of course, they have the resources to get themselves into that highest bidders' club.
So today, we learn that Microsoft's best, most advanced and up to date security features are broken. VUPEN is already advertising and selling malware kits offering the buyer exclusive access to everything on your Windows 8 machine. Worst of all, Microsoft will probably remain unable to patch these vulnerabilities, whose nature is so closely guarded by the baddies. On the other hand, that does limit the number of agents able to exploit these holes - you might see that as a kind of mitigation.
Hat tip: TheNextWeb
Friday 26 October 2012
Music Does Not Commute
 Hey Guitarists
Hey GuitaristsYou know about open string harmonics, right? How you can lightly touch say the bottom E string in the region of the 12th fret (the one just right of the two dots in this Wikipedia diagram), and plucking it, obtain a curiously muted octave note? Somehow softer in timbre than actually playing the fret in the usual way, but unmistakably the same note. That's because the 12th fret is positioned at a point exactly half way up the length of the string, so playing it has the same result, in audio frequency terms, as exciting the string's second harmonic (the red curve marked 2), aka its first overtone, using the light touch trick.
Of course, I'm ignoring the slight stretching of the string caused by pushing it down and on to the fingerboard. So far, so good. And you probably know about the 5th and 7th fret tricks too, right? How the node at the 5th (yellow curve 4) gives you another E, yet another octave up. And how the 7th (orange 3) rings out with a perfect fifth B, this time one octave up from the result of actually playing that fret in the usual way?
Wrong!
Actually those nodes do work as advertised, and the harmonics they produce are just perfect octaves and fifths. However, they are not positioned above the 5th and 7th frets. Because western semitones, specifically the 12 frets in a guitar octave or the 12 keys in a keyboard one, are evenly tempered, i.e., distributed in frequency terms, everything else - everything that isn't an interval of one or more octaves - is just an approximation.
Let's see why. If the perfect fifth interval between E and B corresponded to exactly seven frets, and we strung together twelve such intervals, then we should end up a total of...
7 frets in an interval × 12 intervals = 84 fretsabove our starting point, corresponding to a leap of seven octaves:
12 frets in an octave × 7 octaves = 84 frets.Incidentally, if you find it difficult as I do to imagine a design for a guitar with 84 frets, you might find it helpful to switch to a piano analogy at this point...
Pythagorean Commas
Now consider the sum harmonically. Each perfect fifth interval, say from E up to B, represents a 50% increase in frequency. In other words, the B note, expressed in Hertz (cycles per second), is 1½ times the value of the E. String together twelve such intervals, and you have a frequency multiplication factor of
(3/2) ^ 12 = 3^12 ÷ 2^12 = 531441 ÷ 4096 = 129.75to two decimal places. That's quite different from the expected value for seven octaves,
2^7 = 128.00This difference is known as the Pythagorean Comma, and works out at about 1.36%. The implication is that western music, as rendered on guitars and pianos anyway, is not mathematically commutative! We use that seventh evenly tempered fret, or key, as a perfect fifth interval. But if twelve such intervals (12×7 semitones) amount to something different from seven octaves (7×12 semitones), then something has to give. Because it just doesn't add up. Or rather, divide out. To unity.
 |
From Wikipedia: http://en.wikipedia.org/wiki/Pythagorean_comma |
perfect fifth = 3÷2Historical Note (heh)
seventh fret = 2 ^ (7÷12)
perfect fifth ÷ seventh fret = 1.0011298906275257736
Prior to being written about by me, the calculation of the Pythagorean Comma was also documented in the Chinese (Han dynasty, 122 BC) philosophical classic work The Huainanzi, subsequently extended by Jing Fang (50 BC), then agonized over by centuries' worth of frustrated piano tuners. It gets its contemporary name from its description in The Division of the Canon, an ancient Pythagorean treatise on the relationship between mathematics and acoustics.
Thursday 18 October 2012
Streamed Music Services
Best In Show
The Register Hardware today published a snapshot comparison table showing how a dozen streaming music services compare to each other. Now, a table is a very fine thing indeed, and a reliable statistician's friend. But you and I prefer pictures, right? So I decided to analyse the data provided, using my own personal and completely arbitrary criteria for preferences and priorities. The aim was to reduce each service evaluation to a single number, and so rank them to help decide which I should select - when the day arrives, and I step over my own cold corpse, to sign and pay up for online music. Spoiler: Deezer wins.
Explanatory note: I do pay for music: offline music. Physical media, which I then own, and don't lease from anyone.
How They're Ranked
Okay, so you're a typical streaming music box. How do you earn my favour?
Well, you start from your base score, which is just the number of tracks offered by your service, in millions. So for example at today's levels, Xbox Music leads the field at this stage with 30, while Spotify and Last.fm currently trail on 18 and 12 respectively. Then, you try to earn bonuses.
The first available bonus, 10%, is for services supported on both web and desktop app platforms. If you have only an app, or only web support, you get zut.
Secondly, we look at mobile support. Almost everyone supports Android and iOS. But Rara is Android only, while the iOS offering by Grooveshark requires a jailbreak, and those by Samsung and Xbox are not quite ready yet, so they lose 10%. Conversely, services offering additional mobile coverage, such as BlackBerry, Palm, Symbian, WebOS and/or Windows Phone, get a token 5% bonus for trying a little harder. Similarly for those with additional, non-mobile platforms such as smart TVs, cable, or non-native game consoles.
You don't have an offline mode? Sorry, that's a 10% tax. My advice to you would be shut up and accept this, the appeal court will only double it to punish your insolence. Why shouldn't I be able to hear the music I've paid for, it will say, on my frequent hiking trips to Dunnet Head?
Finally, there's your price. I regard a standard (non-premium) monthly subscription of £5 as quite reasonable for an unlimited, on-demand, streamed music service. If you disagree (Samsung, Xbox) then help yourself to a 50% kick in the nuts. If on the other hand you think £5 is too much (Deezer, Grooveshark, Last.fm) here's a free cuddly toy and a 25% boost for your awesomeness.
For future reference: I'm likely to introduce a massive penalty for Facebook buy-in. Please, just stop it, all of you.
The Results
La France-based Deezer is my surprise winner, scoring over 26; Spotify the more predictable second, at just shy of 19. Then there's little to choose between Grooveshark, Napster, Pure Music, Rdio and Sony. And, it has to be said, what a thoroughly unimpressive lot they all are!
The Register Hardware today published a snapshot comparison table showing how a dozen streaming music services compare to each other. Now, a table is a very fine thing indeed, and a reliable statistician's friend. But you and I prefer pictures, right? So I decided to analyse the data provided, using my own personal and completely arbitrary criteria for preferences and priorities. The aim was to reduce each service evaluation to a single number, and so rank them to help decide which I should select - when the day arrives, and I step over my own cold corpse, to sign and pay up for online music. Spoiler: Deezer wins.
Explanatory note: I do pay for music: offline music. Physical media, which I then own, and don't lease from anyone.
How They're Ranked
Okay, so you're a typical streaming music box. How do you earn my favour?
Well, you start from your base score, which is just the number of tracks offered by your service, in millions. So for example at today's levels, Xbox Music leads the field at this stage with 30, while Spotify and Last.fm currently trail on 18 and 12 respectively. Then, you try to earn bonuses.
The first available bonus, 10%, is for services supported on both web and desktop app platforms. If you have only an app, or only web support, you get zut.
Secondly, we look at mobile support. Almost everyone supports Android and iOS. But Rara is Android only, while the iOS offering by Grooveshark requires a jailbreak, and those by Samsung and Xbox are not quite ready yet, so they lose 10%. Conversely, services offering additional mobile coverage, such as BlackBerry, Palm, Symbian, WebOS and/or Windows Phone, get a token 5% bonus for trying a little harder. Similarly for those with additional, non-mobile platforms such as smart TVs, cable, or non-native game consoles.
You don't have an offline mode? Sorry, that's a 10% tax. My advice to you would be shut up and accept this, the appeal court will only double it to punish your insolence. Why shouldn't I be able to hear the music I've paid for, it will say, on my frequent hiking trips to Dunnet Head?
Finally, there's your price. I regard a standard (non-premium) monthly subscription of £5 as quite reasonable for an unlimited, on-demand, streamed music service. If you disagree (Samsung, Xbox) then help yourself to a 50% kick in the nuts. If on the other hand you think £5 is too much (Deezer, Grooveshark, Last.fm) here's a free cuddly toy and a 25% boost for your awesomeness.
For future reference: I'm likely to introduce a massive penalty for Facebook buy-in. Please, just stop it, all of you.
The Results
La France-based Deezer is my surprise winner, scoring over 26; Spotify the more predictable second, at just shy of 19. Then there's little to choose between Grooveshark, Napster, Pure Music, Rdio and Sony. And, it has to be said, what a thoroughly unimpressive lot they all are!
Monday 15 October 2012
Ribbon Principles
Just Say No
This is a follow-up to my previous article on the Microsoft Office 2007 ribbon style of user interface (UI). It's prompted by a too-long history of design meetings where apparently everything must be reset to a previous decade, and where new people drop in to ask the same fundamental questions yet again, proposing top-of-the-head suggestions that have already been comprehensively discounted by thorough and painstaking research. A blank slate isn't always the best point of departure.
I've listed a very few, key takeaways from Jensen Harris's presentation on the history and evolution of the ribbon UI. The technology is well matured by now, and these caveats, or something like them (preferably a smallish superset), need to become integral to the our new jumping-off point.
No to the Ribbon (sometimes)
The ribbon was never just a fad to be copied, for the sake of looking like Office 2007. For many applications, those containing a few dozen operations, the menu and toolbar approach is still superior - and using a ribbon just looks silly. It's only when you migrate closer to the region of 50, 100 or more unique user-executable commands, that you should be thinking of switching to this more fluent alternative. Remember, Microsoft were driven to develop this UI by the sheer, exponentially, ever-increasing bloat in the numbers of nested menus, toolbars and task panes, in Office 2003 and its immediate predecessors.
No to Command-Oriented Design
Microsoft's Office 2007 group emphasised instead Results-Oriented Design:
You don't just "ribbonise" a form, any more than you "webify" an arbitrary desktop application. The most visible part of this UI design, the ribbon itself, must be supported by a host of other equally essential concepts and devices:
What's missing is as important as what's provided. With the ribbon scheme, Microsoft got rid of more than just the endlessly proliferating dockable multilevel menus and toolbars on every side of the display; also gone is the stack of task panes. Why? Added complexity, for one thing. Task panes don't actually replace anything, they just occupy more space, less productively, giving the user yet another place to search for functionality. Remember, one of the biggest ideas behind the ribbon is having a single point of access for that functionality.
Also: in Office 2003, everybody wanted to add a whole new task pane to the stack, for just their one feature.
No to Customisation
It can seem arrogant to lock down the UI, preventing users from arranging their toolbars, buttons and menus in their "favourite" configuration, or the one deemed most productivity-enhancing (who decides?) for their specific roles or requirements. In truth, more users hate their toolbar and menu docking freedoms. For example, two features of Office 2000 designed to simplify the UI by modifying it, namely adaptive menus and rafted toolbars, actually added so much complexity and disorientation to the user experience that most customers, especially those in corporate environments, turned both off.
As Jensen Harris puts it, 99% of all users' requirements were met by their eventual "static" ribbon design. But 1% of 200 million customers is still two million people; so, the status bar, and a single customisable toolbar, were left in for just those 1%. The point to note is that Microsoft in 2007 were in the happy position of having amassed so much customer feedback (over 3 billion data sessions collected from Office users; 2 million sessions and 40 million command bar clicks per day; 6000 individual data points; etc.), they didn't have to hypothesise about such things - they just looked at the data. You probably don't have that luxury. So, it's even more important that you allow your pet UI features to be questioned. Ruthlessly tortured, in fact. Probably killed.
No to Exceptions
Design tenets have to be religion. Microsoft's design tenet set in the summer of 2003 looked a bit like this:
This is a follow-up to my previous article on the Microsoft Office 2007 ribbon style of user interface (UI). It's prompted by a too-long history of design meetings where apparently everything must be reset to a previous decade, and where new people drop in to ask the same fundamental questions yet again, proposing top-of-the-head suggestions that have already been comprehensively discounted by thorough and painstaking research. A blank slate isn't always the best point of departure.
I've listed a very few, key takeaways from Jensen Harris's presentation on the history and evolution of the ribbon UI. The technology is well matured by now, and these caveats, or something like them (preferably a smallish superset), need to become integral to the our new jumping-off point.
No to the Ribbon (sometimes)
The ribbon was never just a fad to be copied, for the sake of looking like Office 2007. For many applications, those containing a few dozen operations, the menu and toolbar approach is still superior - and using a ribbon just looks silly. It's only when you migrate closer to the region of 50, 100 or more unique user-executable commands, that you should be thinking of switching to this more fluent alternative. Remember, Microsoft were driven to develop this UI by the sheer, exponentially, ever-increasing bloat in the numbers of nested menus, toolbars and task panes, in Office 2003 and its immediate predecessors.
No to Command-Oriented Design
Microsoft's Office 2007 group emphasised instead Results-Oriented Design:
- Think about features instead of commands
- Present functionality at a higher level
- Illustrate features by their results
- Use galleries to let the user close to the result they want to achieve as quickly as possible
- Visual! Tactile! Responsive!
You don't just "ribbonise" a form, any more than you "webify" an arbitrary desktop application. The most visible part of this UI design, the ribbon itself, must be supported by a host of other equally essential concepts and devices:
- Galleries e.g. for Visual Styles and Pictures
- Live Preview
- Contextual Tabs
- Quick Access Toolbar
- Mini Toolbar
- Enhanced Tooltips
- Enhanced Status Bar
- Live Zoom
- Customisable Status Bar
- KeyTips and Keyboard Navigation
- Streamlined Options
- Context Menus
What's missing is as important as what's provided. With the ribbon scheme, Microsoft got rid of more than just the endlessly proliferating dockable multilevel menus and toolbars on every side of the display; also gone is the stack of task panes. Why? Added complexity, for one thing. Task panes don't actually replace anything, they just occupy more space, less productively, giving the user yet another place to search for functionality. Remember, one of the biggest ideas behind the ribbon is having a single point of access for that functionality.
Also: in Office 2003, everybody wanted to add a whole new task pane to the stack, for just their one feature.
No to Customisation
It can seem arrogant to lock down the UI, preventing users from arranging their toolbars, buttons and menus in their "favourite" configuration, or the one deemed most productivity-enhancing (who decides?) for their specific roles or requirements. In truth, more users hate their toolbar and menu docking freedoms. For example, two features of Office 2000 designed to simplify the UI by modifying it, namely adaptive menus and rafted toolbars, actually added so much complexity and disorientation to the user experience that most customers, especially those in corporate environments, turned both off.
As Jensen Harris puts it, 99% of all users' requirements were met by their eventual "static" ribbon design. But 1% of 200 million customers is still two million people; so, the status bar, and a single customisable toolbar, were left in for just those 1%. The point to note is that Microsoft in 2007 were in the happy position of having amassed so much customer feedback (over 3 billion data sessions collected from Office users; 2 million sessions and 40 million command bar clicks per day; 6000 individual data points; etc.), they didn't have to hypothesise about such things - they just looked at the data. You probably don't have that luxury. So, it's even more important that you allow your pet UI features to be questioned. Ruthlessly tortured, in fact. Probably killed.
No to Exceptions
Design tenets have to be religion. Microsoft's design tenet set in the summer of 2003 looked a bit like this:
- A person's focus should be on content, not on the UI. Help people work without interference.
- Reduce the number of choices presented at any given time.
- Increase efficiency.
- Embrace consistency, but not homogeneity.
- Give features a permanent home. Prefer consistent-location UI over "smart" UI.
- Straightforward is better than clever.
Friday 12 October 2012
The "Ribbon" User Interface
Update: someone suggested this article has appeared five years too late. Clearly not a Raymond Chen reader.
Caution!
We have added the Microsoft Office 2007 "Ribbon" style of User Interface (UI) to a number of our products in recent years. The results have ranged from the frankly perfunctory, in the case of our internal or consultants' tools, to the very professional, as with all of our high profile market offerings. In this process, we discovered a great number of troublesome issues, difficult decisions, points of contention, and design dilemmas. All of which, I hasten to add, are a good thing.
This is not a conversion that can be approached lightly, since - particularly by comparison with traditional menus and toolbars - the Ribbon UI:
Caution!
We have added the Microsoft Office 2007 "Ribbon" style of User Interface (UI) to a number of our products in recent years. The results have ranged from the frankly perfunctory, in the case of our internal or consultants' tools, to the very professional, as with all of our high profile market offerings. In this process, we discovered a great number of troublesome issues, difficult decisions, points of contention, and design dilemmas. All of which, I hasten to add, are a good thing.
This is not a conversion that can be approached lightly, since - particularly by comparison with traditional menus and toolbars - the Ribbon UI:
- takes away so much of the user's freedom;
- eliminates "multiple ways" to execute actions;
- removes the comfortable familiarity a user has built up with your app over the years;
- occupies a bigger chunk of valuable screen real estate than the scheme it replaces.
Tuesday 2 October 2012
SCARB Does Security!
A Good End to the Day
Today I led SCARB, our internal Security Coding and Architecture Review Board, in a software security related meeting. As always seems to be the case, I found the agenda changing repeatedly up to and including half an hour before the start. Now that I think of it, in fact that agenda actually kept changing after the start of the meeting, too...
But that wasn't a bad thing! Thanks in part to the vagaries of the way these meetings are set up and run, we ended up with a larger than usual committee, and with representatives from across several different projects: Windows Forms, Web, and both; CQRS and relational; old and new. My presentation, detailing a good half dozen specific security related issues - and their mitigation - in one project, drew comments about the desirability of software and system security reviews in practice, and specifically mentioning the obvious advantages of starting such processes at the same time as the projects themselves.
People seem to particularly like concrete examples. Now, to obtain examples from your own code base, you have to have done a partial security review already. Which was in fact the case for us, at least with two of the projects concerned. Both had previously been taken into the stages of developing a data flow diagram of the system, and of identifying processes, data stores, data flows and the trust boundaries where the vulnerability categories must be investigated.
Now I know what I need to get buy-in, and push the review process further. More examples! SQL injection attacks that work and are demonstrable. XSS attacks, likewise. These can be taken from many resources available around the Internet, but I guess the closer to your own app in terms of applicability, the better. They'll also provide an excellent way of opening the mind to the plethora of attack vectors available to the attacker, encouraging the inclusive, brainstorming, "yes - and..." approach vital to the success of the review process.
And next time, we will have a game of cards.
Today I led SCARB, our internal Security Coding and Architecture Review Board, in a software security related meeting. As always seems to be the case, I found the agenda changing repeatedly up to and including half an hour before the start. Now that I think of it, in fact that agenda actually kept changing after the start of the meeting, too...
But that wasn't a bad thing! Thanks in part to the vagaries of the way these meetings are set up and run, we ended up with a larger than usual committee, and with representatives from across several different projects: Windows Forms, Web, and both; CQRS and relational; old and new. My presentation, detailing a good half dozen specific security related issues - and their mitigation - in one project, drew comments about the desirability of software and system security reviews in practice, and specifically mentioning the obvious advantages of starting such processes at the same time as the projects themselves.
People seem to particularly like concrete examples. Now, to obtain examples from your own code base, you have to have done a partial security review already. Which was in fact the case for us, at least with two of the projects concerned. Both had previously been taken into the stages of developing a data flow diagram of the system, and of identifying processes, data stores, data flows and the trust boundaries where the vulnerability categories must be investigated.
Now I know what I need to get buy-in, and push the review process further. More examples! SQL injection attacks that work and are demonstrable. XSS attacks, likewise. These can be taken from many resources available around the Internet, but I guess the closer to your own app in terms of applicability, the better. They'll also provide an excellent way of opening the mind to the plethora of attack vectors available to the attacker, encouraging the inclusive, brainstorming, "yes - and..." approach vital to the success of the review process.
And next time, we will have a game of cards.
Thursday 27 September 2012
Prokofiev, Stravinsky, Shostakovich
 |
| Prokofiev (Soviet stamp, 1991 centenary) |
If the key to building up a coherent collection of classical music is to have some kind of structure, some skeleton of dry bones on which to hang the meat, then Project Listen To A Crapload Of Symphonies, which started out as my Symphonic listening project before swelling to incorporate concerti, symphonic (tone) poems and ballets, surely qualifies. From an origin point provided by The 100 Greatest Classical Symphonies at Digital Dream Door (which I'll call D3), this bonework has mushroomed, like a badly mixed metaphor, to include at last count over 350 works of enormous merit. Having now completed its genesis of hyper inflation, the list has moved into an era of sustained, steady, but perceptibly accelerating growth.
Of course it still has boundaries. I'm pretty sure I've included nearly all the great symphonists who will ever make it into the list. Though many gifted, modern composers still till the croft, these practitioners are no longer symphonic specialists¹. Similar remarks apply to the concerto. Tone (or symphonic) poems, despite thriving more in modern music, are still limited by the general unpopularity of the genre², ballets even more so. And I don't intend to add any opera to it; my primary interest is instrumental music, not songs.
 |
| Stravinsky (Ukrainian stamp, 2007) |
No, the main area of feature creep is completism - the gradual incorporation of a composer's entire repertoire. Mozart write over 50 symphonies, Haydn more than 100; quite often, it is instructive to consider relationships, similarities and differences between the individual opera (in the sense: plural of opus) of a given maestro. Particularly when the composer and his long form works are already among your favourites at the very outset. So it is for me, with the great Russian triumvirate of Sergei Sergeyevich Prokofiev, Igor Fyodorovich Stravinsky, and Dmitri Dmitriyevich Shostakovich.
Three out of seven Prokofiev symphonies (ignoring revisions) were included in the original D3 list. Two out of four Stravinskys. And six out of fifteen Shostakoviches in the top 120, although an additional two are found bubbling under as the BRMB used to say. That's just not enough! Yet where are we to insert the others, and who or what has to be thrown out to make room for them? Worse still, what about the other composers already on the list, whose excluded works we are still to hear? And worst of all, what of composers not yet listed? Can we be sure that our favourites merit precedence above all of these?
 |
| Shostakovich (Russian stamp, 2000) |
Obviously not without having already heard every work, both on and off the list, and compared each to every other. But the whole purpose of the list was just to start that very process!
Xорошо, let all additions occur at the bottom of the list until we get a feel for it. And anyway, I still don't feel confident rating even the best known symphonies against each other. I still think Beethoven's sixth (Pastorale) is the best thing since baked wheat, yet it's only at number seven. Ho-hum.
Devil take HTML table editing; I'll maintain the symphony list in a Google Docs spreadsheet here. Later I'll add the concerti, etc. Update: done.
Prokofiev
Wikipedia describes Prokofiev as an iconoclastic composer-pianist, a notoriously, ferociously dissonant virtuoso, who after the revolution left Russia for USA and then Europe. There in 1936, increasing economic deprivation prompted a return to Russia, where in response to the 1941 Nazi invasion, he wrote the opera War and Peace. In 1948 his "anti-democratic formalism" saw his income severely curtailed, and he was forced to compose Stalinist works.
Stravinsky
With perhaps the least politically troubled life³ of our three Russian heroes, Stravinsky too lived in Europe (France) and USA (West Hollywood) at different times. He had inexhaustible desire to explore and learn about art, literature and life, and enjoyed many high profile collaborations, particularly while living in Paris. It was in the 1950s that he began to experiment with Schoenberg's tone rows in his compositions.
Shostakovich
Both Prokofiev and Stravinsky, as well as Gustav Mahler, were initially strong influences on Shostakovich, who subsequently developed his own "hybrid" style, easily fusing post-romantic elements with the neo-classical. In later life, chronic ill health, including polio and several heart attacks, permeated his works with a sense of mortality. After suffering a series of falls, he wrote jokingly:
Target achieved so far: 75% (right leg broken, left leg broken, right hand defective. All I need to do now is wreck the left hand and then 100% of my extremities will be out of order.Well, perhaps he did, but then found himself unable to write about it.
¹ Shostakovich, 1906-1975, has been called The last great symphonist.
² Classical music, by de facto definition, is not popular music.
³ Although he was famously threatened with a $100 fine for adding an unconventional major seventh chord to The Star Spangled Banner!
Tuesday 25 September 2012
Windows 8 Bootkit
UEFI Technology: Say Hello to the Windows 8 Bootkit!
Writing a bootkit couldn't be an easier task for virus writers with the UEFI framework available, much easier than before when they needed to code in pure assembly.ITSEC director Marco Giuliani sounds less than impressed by the security of the Windows 8 kernel, specifically its porting of the legacy BIOS firmware and Master Boot Record (MBR) into the new Unified Extensible Firmware Interface (UEFI), first fully supported by Microsoft in 64-bit Windows 7. Here he is referring to the fact that UEFI provides a C development environment option, whereas assembly language skills were mandatory for VXers in BIOS days.
http://www.itsec.it/2012/09/18/uefi-technology-say-hello-to-the-windows-8-bootkit/This isn't the first Windows 8 bootkit to emerge. Last year, Vienna-based Peter Kleissner's Stoned and Stoned Lite proved the concept of loading boot malware from a USB or CD drive on older machines, However these kits didn't circumvent the UEFI. Now this has been shown to be trivial, the only remaining line of defence is to enable SecureBoot by default - an option which many critics complain could limit or even prevent the installation of such alternatives as Linux and FreeBSD.
Thursday 20 September 2012
Simple Regex #6½: More Lazy Quantifiers
Hush. Hush.
The security-related components of my work continue to comprise only product-specific threats and mitigation, which means I can't exactly blog about them in a public forum like this one. Instead, here's a little more on the subject of that previous application of Regular Expressions to music catalogues.
Oh and about that previous article, I have to be honest and say that I've been getting complaints! Apparently the level of explanation offered wasn't even up to my usual low standards of lucidity? Let's try to rectify that here. The goal you'll remember was to parse a list of classical music pieces like this,
It helps to apply these two visual filters when inspecting the various groups in patterns like the third line above:
 More Music Maestro!
More Music Maestro!
Hopefully that's as much analysis as we need for this pattern. It's a little more complex than previously, because of the addition of this opus/catalogue number field, appearing when I generalised the listening project, originally featuring just symphonies, to include also the concerti, symphonic poems and ballets in the following lists:
The security-related components of my work continue to comprise only product-specific threats and mitigation, which means I can't exactly blog about them in a public forum like this one. Instead, here's a little more on the subject of that previous application of Regular Expressions to music catalogues.
Oh and about that previous article, I have to be honest and say that I've been getting complaints! Apparently the level of explanation offered wasn't even up to my usual low standards of lucidity? Let's try to rectify that here. The goal you'll remember was to parse a list of classical music pieces like this,
49. Violin Concerto in E major, RV271 "L'amoroso" - Antonio Vivaldisubject to the proviso that while an item's rank (here equal to 49), title (Violin Concerto) and composer name (Antonio Vivaldi) are all mandatory, the key (E major), opus/catalogue number (RV271) and nickname (L'amoroso) are all optional. Here's an analysis of the Regex pattern I'm using to split these records into fields:
The @ symbol is an artifact of the C# language. Most of its appearances above are redundant, but regardless, I do tend to use it habitually when working with Regex. It saves having to double all backslashes. So the first lineprivate const string rank = @"(\d+)\."; private const string title = @" (.+?)"; private const string key = @"(?: in ([A-G](?: flat| sharp)?(?: major| minor)?))?"; private const string number = @"(?:, (.+?))?"; private const string nickname = @"(?: ""(.+)"")?"; private const string composer = @" - (.+)"; private const string pattern = rank + title + key + number + nickname + composer;
matches one or more decimal digits (followed by a literal period, which is outside the capturing parentheses, and so doesn't itself get included in the captured group). The second lineprivate const string rank = @"(\d+)\.";
matches a space (again excluded, being outside the group) followed by one or more characters of the title, but matching as few characters as possible consistent with an overall successful match.private const string title = @" (.+?)";
It helps to apply these two visual filters when inspecting the various groups in patterns like the third line above:
(?: starts a non-capturing group;So for example, the overall key group pattern above is both non-capturing, since it starts with (?:, and optional, since it ends with )?. Nested within it is the main capturing group (labelled c1 in the expanded analysis below) for the key text, and nested in turn within that are two further, non-capturing, optional groups, n1 and n2:
)? ends an optional group.
private const string n1 = @"(?: flat| sharp)?"; private const string n2 = @"(?: major| minor)?"; private const string c1 = @"([A-G]" + n1 + n2 + ")"; private const string key = @"(?: in " + c1 + ")?";
 More Music Maestro!
More Music Maestro!Hopefully that's as much analysis as we need for this pattern. It's a little more complex than previously, because of the addition of this opus/catalogue number field, appearing when I generalised the listening project, originally featuring just symphonies, to include also the concerti, symphonic poems and ballets in the following lists:
- Symphonies (129)
- Concerti (60 piano, 50 violin, 40 other)
- Tone Poems (50)
- Ballets (16)
106. Symphony No. 14 for soprano, bass, strings, and percussion – Dmitri ShostakovichI just deleted them. Well sometimes, and particularly with Regex, the best solution is to get a life.
Wednesday 5 September 2012
Simple Regex #6: Lazy Quantifiers
Dedicated Listener
I've decided to listen to 129 classical symphonies and rate them against each other, to try to understand this musical format a little better. The project has two immediate side effects of a technical nature. I've had to:
The latter side effect occurs because I've arrived at my list of 129 symphonies under test by combining the main table of 120 listed at Digital Dream Door,
Now, it would have been easy to take multiple passes at this task, first removing any optional (key and nickname) fields present, then splitting the remaining text into the mandatory rank, root title and composer name fields. Too easy, in fact. Why do that, when we could just use a single Regex pattern to simultaneously extract the full compliment of fields, mandatory and optional?
Too Greedy
The difficulty is that the pattern capturing the symphony title could also gobble up any key and/or nickname information that might be present. Let's say for simplicity that the key field can be identified by the word in, while the nickname is delimited by double quotation marks. That gives us two optional groups:
Dieting
Quantifiers like ?, *, + and {m,n} can be made less greedy by following them with a question mark. For example, the ? quantifier on its own matches zero or one occurrence(s) of the preceding expression, but with a preference for one. That's to say, it will gobble up input characters whenever it can. ?? also matches zero or one occurrence(s) of the expression immediately before it, but with a preference for zero. In general, these so-called lazy quantifiers consume as few input characters as possible, while still letting the overall pattern match succeed. Which turns out to be exactly what's needed in our case:
The final pattern that I used contained many further refinements, including named groups for readability, generalisation of white space, trimming of field contents, and stricter key field matching with a more specific group pattern,
Further Reading, Listening
Greedy and lazy Regex quantifiers are explained in more detail at MSDN:
43 56 symphonies on Brian's list, including all of his top 20 25 (and quite a few duplicates; who authorised that?). So cost wise, I'm exactly one third almost half complete. Although to be honest, I've never really liked Solti's limp wristed walkthrough of Mozart's Jupiter...
I've decided to listen to 129 classical symphonies and rate them against each other, to try to understand this musical format a little better. The project has two immediate side effects of a technical nature. I've had to:
- Replace the 32GB SDHC card on my
phoneMP3 player, a venerable Sony Ericsson Xperia X10 Mini, with the bleeding edge Sandisk 64GB SDXC, to make room for a shedload of symphonies; and - Brush up on greedy quantifiers, and their lazier, more reluctant counterparts.
The latter side effect occurs because I've arrived at my list of 129 symphonies under test by combining the main table of 120 listed at Digital Dream Door,
http://www.digitaldreamdoor.com/pages/best-classic-symp.htmlwith a further 9 also-rans suggested by that forum's moderator, and compiler of the main list, whom we shall call Brian (for that is his name). Having screen scraped his raw data, converting all its en–dashes and “directional quotes” to hy-phens and "neutrals", I was left with the task of parsing these results. Here's a small sample:
1. Symphony No. 9 in D minor "Choral" - Ludwig Van BeethovenFor analysis, I need to extract certain data from these entries. The first, dot-terminated field is Brian's initial rank. This is followed by the full title of the symphony, which usually includes its performance key, and sometimes a popular alternate title or nickname. Finally, a hyphen sets off the composer name.
2. Symphony No. 5 in C minor - Ludwig Van Beethoven
11. Symphonie Fantastique - Hector Berlioz
63. Symphony No. 3 "The Camp Meeting" - Charles Ives
Now, it would have been easy to take multiple passes at this task, first removing any optional (key and nickname) fields present, then splitting the remaining text into the mandatory rank, root title and composer name fields. Too easy, in fact. Why do that, when we could just use a single Regex pattern to simultaneously extract the full compliment of fields, mandatory and optional?
Too Greedy
The difficulty is that the pattern capturing the symphony title could also gobble up any key and/or nickname information that might be present. Let's say for simplicity that the key field can be identified by the word in, while the nickname is delimited by double quotation marks. That gives us two optional groups:
(?: in (.+?))?
(".+")?(\d+)\. (.+)(?: in (.+?))?(".+")? - (.+)Dieting
Quantifiers like ?, *, + and {m,n} can be made less greedy by following them with a question mark. For example, the ? quantifier on its own matches zero or one occurrence(s) of the preceding expression, but with a preference for one. That's to say, it will gobble up input characters whenever it can. ?? also matches zero or one occurrence(s) of the expression immediately before it, but with a preference for zero. In general, these so-called lazy quantifiers consume as few input characters as possible, while still letting the overall pattern match succeed. Which turns out to be exactly what's needed in our case:
(\d+)\. (.+?)(?: in (.+?))?(".+")? - (.+)The final pattern that I used contained many further refinements, including named groups for readability, generalisation of white space, trimming of field contents, and stricter key field matching with a more specific group pattern,
which actually removes the need for the second lazy quantifier above. Incidentally this also allows the word in to appear in the symphony's title in a non-key, non-nickname context - as for example in Igor Stravinsky's Symphony in Three Movements, which happens to be number 76 on Brian's list.[A-G](?: sharp| flat)?(?: major| minor)?
Further Reading, Listening
Greedy and lazy Regex quantifiers are explained in more detail at MSDN:
http://msdn.microsoft.com/en-us/library/3206d374.aspxA good online tool for testing regular expressions containing multiple groups is Derek Slager's AJAX offering, A Better .NET Regular Expression Tester, which can be found here:
http://derekslager.com/blog/posts/2007/09/a-better-dotnet-regular-expression-tester.ashxAs for the listening exercise, a quick survey of my dusty old Classic FM CDs reveals that I already have good recordings of
Monday 27 August 2012
Two-Factor Authentication Example: Dropbox
Update: LifeHacker has a list of places where two-factor authentication is currently available as an option.
I'd Go for the App
Generally less accurately referred to as Two-Step Authentication, the principle of Two Factor Authentication demands the production of two or more out of a set of three authentication factor categories:
One of the first two-factor systems to gain popularity was Google's Authenticator app (an open source project) on these platforms:
Now On Dropbox
Anyway, not to bury the lede, Dropbox - perhaps in response to last month's spammage, enabled by a Dropbox employee who had re-used his or her password at another, previously hacked site, resulting in the exposure of many users' email addresses - now offers such a system. Look under the Security tab, in the section labelled Account sign in, for the so-called Two-step verification setting.
Two options are provided for acquiring the new verification code. The first is a simple text message to your mobile phone. This is the easier of the two, but it also introduces a new potential vulnerability. Attackers can use social engineering against your phone provider to have your messages forwarded to another account. This exploit has in fact been documented several times against Google's two-factor system, e.g. at CloudFlare in May of this year.
So yeah, I'd definitely go for option 2, which is to use one of the following mobile apps to generate a unique time-sensitive security code with the help of the standard Time-based One-Time Password (TOTP) algorithm:
Hat tip: Brian Krebs, as is so often the case!
I'd Go for the App
Generally less accurately referred to as Two-Step Authentication, the principle of Two Factor Authentication demands the production of two or more out of a set of three authentication factor categories:
- A knowledge factor - something you know;
- A possession factor - something you have; and
- An inherence factor - something you are.
One of the first two-factor systems to gain popularity was Google's Authenticator app (an open source project) on these platforms:
- Android 2.1 or later;
- iPhone iOS 3.1.3 or later; and
- BlackBerry OS 4.5 - 6.0.
Now On Dropbox
Anyway, not to bury the lede, Dropbox - perhaps in response to last month's spammage, enabled by a Dropbox employee who had re-used his or her password at another, previously hacked site, resulting in the exposure of many users' email addresses - now offers such a system. Look under the Security tab, in the section labelled Account sign in, for the so-called Two-step verification setting.
Two options are provided for acquiring the new verification code. The first is a simple text message to your mobile phone. This is the easier of the two, but it also introduces a new potential vulnerability. Attackers can use social engineering against your phone provider to have your messages forwarded to another account. This exploit has in fact been documented several times against Google's two-factor system, e.g. at CloudFlare in May of this year.
So yeah, I'd definitely go for option 2, which is to use one of the following mobile apps to generate a unique time-sensitive security code with the help of the standard Time-based One-Time Password (TOTP) algorithm:
- Google Authenticator (Android/iPhone/BlackBerry, as mentioned above)
- Amazon AWS MFA (Android)
- Windows Phone Authenticator (Windows Phone 7)
Hat tip: Brian Krebs, as is so often the case!
Wednesday 22 August 2012
Security (Link) Clearance - August 2012
Another small selection of interesting stories from recent security blogs.

Why passwords have never been weaker - and crackers have never been stronger.
Over at Ars Technica, Dan Goodin explains why, thanks to real-world data, the keys to your digital kingdom are under assault:
http://arstechnica.com/security/2012/08/passwords-under-assault/

The iPhone Has Passed a Key Security Threshold
So thinks Technology Review contributing editor Simson L. Garfinkel:
Does society really want extremely private mobile devices if they make life easier for criminals? Apple's newly toughened standards sharpen the focus on that question.
http://www.technologyreview.com/news/428477/the-iphone-has-passed-a-key-security-threshold/

Is iPhone Security Really this Good?
Meanwhile, Bruce Schneier has his own perspective on that assertion:
Yes, I believe that full-disk encryption -- whether Apple's FileVault or Microsoft's BitLocker (I don't know what the iOS system is called) -- is good; but its security is only as good as the user is at choosing a good password.
http://www.schneier.com/blog/archives/2012/08/is_iphone_secur.html

Triple DDoS vs. KrebsOnSecurity
With the best security blog of them all, it's unsurprising that Brian Krebs continues to attract the ire and DDoS arrows of the spambot kings:
According to Prolexic, the one used against KrebsOnSecurity.com was Attack Type 4, a.k.a “Max Flood”; this method carries a fairly unique signature of issuing POST requests against a server that are over a million bytes in length.
http://krebsonsecurity.com/2012/08/triple-ddos-vs-krebsonsecurity/

There ya go.

Why passwords have never been weaker - and crackers have never been stronger.
Over at Ars Technica, Dan Goodin explains why, thanks to real-world data, the keys to your digital kingdom are under assault:
http://arstechnica.com/security/2012/08/passwords-under-assault/

The iPhone Has Passed a Key Security Threshold
So thinks Technology Review contributing editor Simson L. Garfinkel:
Does society really want extremely private mobile devices if they make life easier for criminals? Apple's newly toughened standards sharpen the focus on that question.
http://www.technologyreview.com/news/428477/the-iphone-has-passed-a-key-security-threshold/

Is iPhone Security Really this Good?
Meanwhile, Bruce Schneier has his own perspective on that assertion:
Yes, I believe that full-disk encryption -- whether Apple's FileVault or Microsoft's BitLocker (I don't know what the iOS system is called) -- is good; but its security is only as good as the user is at choosing a good password.
http://www.schneier.com/blog/archives/2012/08/is_iphone_secur.html

Triple DDoS vs. KrebsOnSecurity
With the best security blog of them all, it's unsurprising that Brian Krebs continues to attract the ire and DDoS arrows of the spambot kings:
According to Prolexic, the one used against KrebsOnSecurity.com was Attack Type 4, a.k.a “Max Flood”; this method carries a fairly unique signature of issuing POST requests against a server that are over a million bytes in length.
http://krebsonsecurity.com/2012/08/triple-ddos-vs-krebsonsecurity/

There ya go.
Thursday 9 August 2012
Eliot Reads Prufrock
I Come In Value Packs Of Ten
The Love Song of J Alfred Prufrock, by Thomas Stearns Eliot, is my favourite poem. Not that I've read them all, I mean all the poems in the world, before arriving at this objective decision; that is not what I meant at all. There are far too many poems in existence to have done that, seriously, there's literally dozens out there. But of the five or six that I have read, Prufrock is quite definitely the best.
So I quite enjoy listening to the poet's own recitation, and ever since playing the old vinyl record at a friend's house in about 1980, have always been within a lodger's lunge of such a recording. Today, deciding to legalise our relationship, this poem and me, I grabbed a few spoken word MP3s from Amazon: The Waste Land, a scratchy old clipping suite encoded at an average of 62¼ kbps (and extravagant at that if you ask me); Prufrock itself; and one other, The Triumphal March From Coriolan.
Immediately, the 20 minute duration of the Prufrock file caught my attention. You see, Prufrock is my party piece. Well, it's either that or a Pogues-informed The Band Played Waltzing Matilda, Eric Bogle's despairing Gallipoli dirge, which nevertheless does have the advantage of being an actual song. No, I don't get invited to a lot of parties... you knew? You are not blind! How keen you are! On second thoughts it might be more accurate to describe Prufrock as: the piece I would recite on the night bus home from George Square, in order to ensure my evening ended with a good, sound beating up. Playing relentless Status Quo on your ghetto blaster works almost as well.
But I divest. I knew that, even after ten pints of Stella Artois, there's no way to stammer, slur, stretch and deform a recitation of Prufrock over more than about 10 of those 20 minutes. So what was going on? Firing up foobar2000, I discovered that both of the higher bit rate files contained multiple works.
I Call That A Bargain
01 - The Love Song of J Alfred Prufrock.mp3 actually includes the first three poems (which belong together anyway) from Prufrock and Other Observations, and finishes with Mr. Eliot's Sunday Morning Service. Here's the cue sheet:
00:00 - The Love Song of J Alfred Prufrock
08:20 - Portrait of a Lady
15:35 - Preludes
18:20 - Mr. Eliot's Sunday Morning Service
20:00 - [end]
02 - The Triumphal March From Coriolan.mp3 contains the following:
00:00 - Ash Wednesday
13:45 - A Song for Simeon
16:15 - Marina
18:33 - Triumphal March From Coriolan
21:45 - O Light Invisible (from The Rock)
24:20 - Chorus from Murder in the Cathedral
26:30 - Chorus from The Family Reunion
28:20 - [end]
I guess someone read the original LP's bipartite title, T S Eliot reads The Love Song of J Alfred Prufrock & Triumphal March From Coriolan (link goes to a March 1959 Gramophone review), and decided just to rip and label sides A and B accordingly and respectively. So there you have it: get 'em while they're hot, eight and three-halves poems for the price of two. As for The Waste Land, well those files didn't contain any Easter Eggs. Incidentally if you'd like to hear that latter masterpiece in full, the Harper Audio is rebroadcast in various formats (though not MP3) by the Internet Multicasting Service here, and of course less legally throughout YouTube.
The Love Song of J Alfred Prufrock, by Thomas Stearns Eliot, is my favourite poem. Not that I've read them all, I mean all the poems in the world, before arriving at this objective decision; that is not what I meant at all. There are far too many poems in existence to have done that, seriously, there's literally dozens out there. But of the five or six that I have read, Prufrock is quite definitely the best.
So I quite enjoy listening to the poet's own recitation, and ever since playing the old vinyl record at a friend's house in about 1980, have always been within a lodger's lunge of such a recording. Today, deciding to legalise our relationship, this poem and me, I grabbed a few spoken word MP3s from Amazon: The Waste Land, a scratchy old clipping suite encoded at an average of 62¼ kbps (and extravagant at that if you ask me); Prufrock itself; and one other, The Triumphal March From Coriolan.
Immediately, the 20 minute duration of the Prufrock file caught my attention. You see, Prufrock is my party piece. Well, it's either that or a Pogues-informed The Band Played Waltzing Matilda, Eric Bogle's despairing Gallipoli dirge, which nevertheless does have the advantage of being an actual song. No, I don't get invited to a lot of parties... you knew? You are not blind! How keen you are! On second thoughts it might be more accurate to describe Prufrock as: the piece I would recite on the night bus home from George Square, in order to ensure my evening ended with a good, sound beating up. Playing relentless Status Quo on your ghetto blaster works almost as well.
But I divest. I knew that, even after ten pints of Stella Artois, there's no way to stammer, slur, stretch and deform a recitation of Prufrock over more than about 10 of those 20 minutes. So what was going on? Firing up foobar2000, I discovered that both of the higher bit rate files contained multiple works.
I Call That A Bargain
01 - The Love Song of J Alfred Prufrock.mp3 actually includes the first three poems (which belong together anyway) from Prufrock and Other Observations, and finishes with Mr. Eliot's Sunday Morning Service. Here's the cue sheet:
00:00 - The Love Song of J Alfred Prufrock
08:20 - Portrait of a Lady
15:35 - Preludes
18:20 - Mr. Eliot's Sunday Morning Service
20:00 - [end]
02 - The Triumphal March From Coriolan.mp3 contains the following:
00:00 - Ash Wednesday
13:45 - A Song for Simeon
16:15 - Marina
18:33 - Triumphal March From Coriolan
21:45 - O Light Invisible (from The Rock)
24:20 - Chorus from Murder in the Cathedral
26:30 - Chorus from The Family Reunion
28:20 - [end]
I guess someone read the original LP's bipartite title, T S Eliot reads The Love Song of J Alfred Prufrock & Triumphal March From Coriolan (link goes to a March 1959 Gramophone review), and decided just to rip and label sides A and B accordingly and respectively. So there you have it: get 'em while they're hot, eight and three-halves poems for the price of two. As for The Waste Land, well those files didn't contain any Easter Eggs. Incidentally if you'd like to hear that latter masterpiece in full, the Harper Audio is rebroadcast in various formats (though not MP3) by the Internet Multicasting Service here, and of course less legally throughout YouTube.
Sunday 29 July 2012
Happy Birthday (3) To Me
This Little Blog is Three
Three years behind the masthead. Macro blogging is officially dead, social media in the ascendancy, and still I won't roll down the shutters and scarper. What the hell is wrong with me!
Targets
I can only think it must be love. So then, how's my blogging frequency been holding up? At the 2009 outset, declared goals were:
Unpopularity Analytic
About 1,500 page views per month, last time I checked. Low enough to avoid most comment spammers, but just high enough to retain my interest.
As for the blog's original motivation, namely the introduction of security related software development, that's been superseded by the formation of something called a SCARB group in our (new, extended, all-inclusive and thoroughly democratic) Development Department. When the Security subcommittee (that's me and my pals, the "S" of the group moniker) enters a less dormant phase, this little blog will be one of the first to know.
Previously:
Three years behind the masthead. Macro blogging is officially dead, social media in the ascendancy, and still I won't roll down the shutters and scarper. What the hell is wrong with me!
Targets
I can only think it must be love. So then, how's my blogging frequency been holding up? At the 2009 outset, declared goals were:
- two posts per week, on average;
- half of those technical, half not;
- half of the technical posts to be security related.
Unpopularity Analytic
About 1,500 page views per month, last time I checked. Low enough to avoid most comment spammers, but just high enough to retain my interest.
As for the blog's original motivation, namely the introduction of security related software development, that's been superseded by the formation of something called a SCARB group in our (new, extended, all-inclusive and thoroughly democratic) Development Department. When the Security subcommittee (that's me and my pals, the "S" of the group moniker) enters a less dormant phase, this little blog will be one of the first to know.
Previously:
Happy Birthday To MeBirthday candles courtesy of Wikipedia.
Happy Birthday (2) To Me
Thursday 26 July 2012
RIP Free Cellular Web Access
And A Mystery Solved Thanks To XKCD
My original Amazon Kindle, with its free global access to 3G networks and its experimental browser, was a Christmas gift from my wife, having been inspired by my apparent inability to organise my dead tree storage. This browser uses the same connection that all 3G-equipped Kindles use to download books via Amazon's Whispernet, and until recently, it offered access to as much of the world wide web as you could take. Usually, that wasn't much. The browser renders like treacle, while pages don't look terrific on the monochrome, electronic ink display.
But it was functional, and quite useful on continental holidays and other occasions when we found ourselves temporarily without WiFi access. Just as recently as, well, earlier this very month, I had cause to be grateful for Linda's decisions (-; in both cases, against my better judgement ;-) to buy me (a) a Kindle, (b) with 3G connectivity. Sitting in the garden outside our French gîte, I reached the end of my chosen holiday read (a pulpwood edition of The Hunger Games) and wanted immediately to download its sequels, whilst simultaneously checking out a few blog updates.
That was then. Today, as I read on El Reg, Amazon have started exercising their reserved, small-print right, to throttle this free 3G access at just 50MB per month. Obviously having learned from both the Sony experience and their own previous missteps, they are following this course in preference to just switching off free 3G access altogether.
However...
There still remains a mystery in the detail. This post on the MobileRead forum reports the cutoff message, followed by another:
That's when I remembered the above XKCD cartoon, from 3½ years ago. Click through for the full version. Although the answer isn't in the printed cartoon itself, it's in Randall Munroe's floating text that appears when you hover over it:
My original Amazon Kindle, with its free global access to 3G networks and its experimental browser, was a Christmas gift from my wife, having been inspired by my apparent inability to organise my dead tree storage. This browser uses the same connection that all 3G-equipped Kindles use to download books via Amazon's Whispernet, and until recently, it offered access to as much of the world wide web as you could take. Usually, that wasn't much. The browser renders like treacle, while pages don't look terrific on the monochrome, electronic ink display.
But it was functional, and quite useful on continental holidays and other occasions when we found ourselves temporarily without WiFi access. Just as recently as, well, earlier this very month, I had cause to be grateful for Linda's decisions (-; in both cases, against my better judgement ;-) to buy me (a) a Kindle, (b) with 3G connectivity. Sitting in the garden outside our French gîte, I reached the end of my chosen holiday read (a pulpwood edition of The Hunger Games) and wanted immediately to download its sequels, whilst simultaneously checking out a few blog updates.
That was then. Today, as I read on El Reg, Amazon have started exercising their reserved, small-print right, to throttle this free 3G access at just 50MB per month. Obviously having learned from both the Sony experience and their own previous missteps, they are following this course in preference to just switching off free 3G access altogether.
However...
There still remains a mystery in the detail. This post on the MobileRead forum reports the cutoff message, followed by another:
I got a second message saying that I'd have 24 hours of grace to continue to use 3G for Web browsing, but that after that I could use 3G only for visiting Amazon.com, Wikipedia, and the Kindle Store.Certainly, retaining free access to both Amazon and the Kindle Store makes commercial sense. But why should Wikipedia be particularly exempted?
That's when I remembered the above XKCD cartoon, from 3½ years ago. Click through for the full version. Although the answer isn't in the printed cartoon itself, it's in Randall Munroe's floating text that appears when you hover over it:
I'm happy with my Kindle 2 so far, but if they cut off the free Wikipedia browsing, I plan to show up drunk on Jeff Bezos's lawn and refuse to leave.
Wednesday 25 July 2012
Book Review: Liars & Outliers
 Enabling the Trust that Society Needs to Thrive
Enabling the Trust that Society Needs to ThriveA favourite blog was noticeably subdued of late, while the inestimable Bruce Schneier put his finishing touches to his latest tome. No sooner was he done, however, than all of my favourite blogs burst out with news, reviews, and other expositions about it. Resolved to buy a copy, maybe on Kindle, I nevertheless put in a book request to my manager, and was in due course pleasantly surprised by the hardback landing on my desk.
Surprised? Well, I was unsure whether it would qualify for purchase. It's not a technical book, although it does cover many technical issues we have to deal with in daily business. It's not about programming, or not exclusively so. What it is, is a thorough investigation into the nature of trust within society. Or in other words, into the nature of of civilisation: how it works, and why it doesn't. How indispensable and deeply reaching is trust. How, why, when and where we depend upon it. How our essential systems can be designed to guarantee it. As ever, Bruce's approach to each little corner of the subject matter is almost rigorously scientific, being relatively free from hand waving and equivocation, and as evidence-based as he can diligently achieve.
After an overview, declaring the primary aims of the book, and containing an excellent diagram of the formal terms used (societal dilemma being a central one) and their relationships, the remainder of the book consists of four main sections.
Part I: The Science of Trust
This deals with the various research fields comprising the "background" sciences of the book: experimental and evolutionary psychology, biology, neuroscience, economics, the mathematics of game theory, computer security, and so on. Chapter three will be particularly familiar territory if you've ever studied evolutionary perspectives on behaviour, such as sociobiology. This is followed by a historical view of sociology and societal scaling, then by a return to game theory for an examination of societal dilemmas and the nature of conflict.
Part II: A Model of Trust
This is the most intensely argued and analytically comprehensive section of the book, and it might take more than one reading here and there to follow the workings of the "Model" presented. Clearly this is an exposition of the central concept that inspired the whole work. Various pressures are considered both in isolation and in concert: moral and institutional stresses, considerations of reputation, and the limits imposed by security systems. Schneier's goal is to get you to hold all of these simultaneously in your conception, tracing the interconnections and interplay between them.
In chapter 9, Institutional Pressures, Schneier examines the threats facing modern society. Acknowledging that one of the biggest perceived threats is terrorism, he astutely reminds us we can never ensure perfect security against this. Arguing that America's TSA budget should be measured in the millions, not billions of dollars, he observes that talk of terrorism as an "existential threat" to society is complete rubbish. While terrorism remains sufficiently rare, which it is; and while the vast majority of people survive, which they do; society itself will continue to survive. Yet while this observation remains unarguable, politically it is impossible for our leaders to speak it.
Part III: The Real World
In the second half of the book Schneier describes real world Organisations, Corporations and Institutions, illustrating how the competing interests of these bodies lead to evolution and resolution in certain real world situations. A recurring theme is fishing, which at all levels has rules and quotas adhered to by the majority, but offering considerable profits and a low risk of getting caught to the minority of cheats.
Part IV: Conclusions
To be frank, you could say that there are very few actual conclusions in the book itself. In the chapter on Technology, Schneier proposes a set of design principles for effective societal pressures, one of the key points of the book. But more often, he provides us rather with information, with the background to understand and make sense of that information, and with the grounding in a refreshing number of academic and scientific disciplines that we can exploit to build confidence in our own conclusions, which we are encouraged to reach independently.
In so doing, you're certain find the scope of input presented here quite breathtaking.
Bruce Schneier
Liars and Outliers: Enabling the Trust That Society Needs to Thrive
John Wiley & Sons
17 Feb 2012
ISBN-10: 1118143302
ISBN-13: 978-1118143308
Thursday 19 July 2012
Displaying File Sizes
Readability by Approximation
When it comes to displaying "rough" file sizes (1.2 KB, 34.5 MB, etc), and none of the online solutions offer exactly what you want, then you write your own struct:
When it comes to displaying "rough" file sizes (1.2 KB, 34.5 MB, etc), and none of the online solutions offer exactly what you want, then you write your own struct:
This outputs a consistent three significant figures, with the exception of cases 1000..1023 Bytes, which are output as-is. The supplied set of overloaded operators sufficed for the immediate requirements of my app, which involved only accumulating and subtracting totals, but can obviously be extended easily to include comparisons, multiplication, implicit conversions, etc. Notice the nested calls to string.Format() using escaped {{i.e., doubled-up}} braces, as previously illustrated under C# String Format Run Time Field Width.public struct ByteCount { public long Value { get; set; } public ByteCount(long value) : this() { Value = value; } public static ByteCount operator + (ByteCount x) { return x; } public static ByteCount operator - (ByteCount x) { return new ByteCount(-x.Value); } public static ByteCount operator + (ByteCount x, ByteCount y) { return x + y.Value; } public static ByteCount operator + (ByteCount x, long y) { return new ByteCount(x.Value + y); } public static ByteCount operator + (long x, ByteCount y) { return y + x; } public static ByteCount operator - (ByteCount x, ByteCount y) { return x + -y; } public static ByteCount operator - (ByteCount x, long y) { return x + -y; } public static ByteCount operator - (long x, ByteCount y) { return x + -y; } public override string ToString() { const string units = "EPTGMK"; var unitSize = 1L << 10 * units.Length; foreach (var unit in units) { if (Value >= unitSize) { var value = decimal.Divide(Value, unitSize); return string.Format( string.Format( "{{0:{0}}} {{1}}B", value >= 100 ? "#" : value >= 10 ? "#.#" : "#.##"), value, unit); } unitSize >>= 10; } return string.Format("{0} Bytes", Value); } }
Subscribe to:
Posts (Atom)













